What You Need to Provide
To start receiving PRESS events, provide the following during onboarding:| Item | Description |
|---|---|
| Webhook URL | Your HTTPS endpoint that will receive events (e.g., https://api.yourdomain.ae/webhooks/press). Must support POST requests. |
| Static IP | Your server’s public IP address. ICP whitelists this for secure connectivity. |
| Event Subscriptions | Which events you want to receive. You can subscribe to all or a subset. See Lifecycle Events. |
| Technical Contact | Email address of the person responsible for implementing and maintaining the webhook integration. |
| Support Contact | Email address for incident and operational communication. |
What ICP Returns
Once onboarding is complete, you receive:| Item | Description |
|---|---|
| HMAC Signing Secret | A unique secret key prefixed whsec_ used to verify every incoming webhook request. Download it from the UAE KYC client dashboard. |
| Subscription ID | Your unique webhook subscription identifier. Included in every delivery header. |
| Sandbox Credentials | A separate secret and subscription for testing before going live. |
Endpoint Requirements
Your webhook endpoint must:- Serve over HTTPS (TLS 1.3 only). HTTP is not supported.
- Accept POST requests.
- Accept
Content-Type: application/cloudevents+json. - Be reachable from the ICP webhook delivery service.
- Respond with HTTP
200within 500 milliseconds. - Not depend on redirects — ICP does not follow
3xx. - Not require interactive login or authentication challenges.
Security
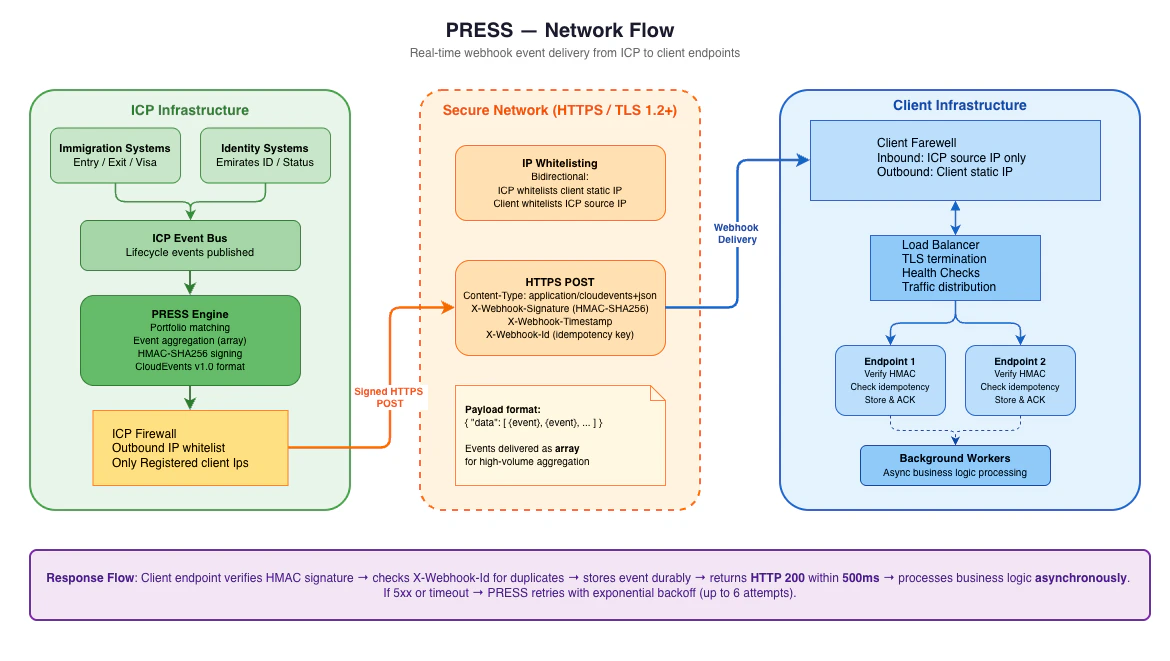
IP Whitelisting
| Direction | What is whitelisted |
|---|---|
| ICP → You | ICP shares their source IP with you. Whitelist it on your firewall or load balancer so you only accept traffic from ICP. |
| You → ICP | Your static IP is whitelisted at ICP. Only traffic to your whitelisted IP will be serviced. |
HMAC Signature
Every webhook delivery includes anX-Webhook-Signature header. This is an HMAC-SHA256 signature computed over the request body using your signing secret. You must verify this on every request.
See Signature Verification for the full verification guide and code examples.
Sandbox Checklist
Complete all of these before requesting production activation:Endpoint receives and parses webhook requests correctly
Endpoint receives and parses webhook requests correctly
Send test events from sandbox and confirm your endpoint parses all event types without errors.
HMAC signature verification works
HMAC signature verification works
Deliberately send a request with a bad signature and confirm your endpoint rejects it with
401.Replay protection is implemented
Replay protection is implemented
Reject requests where the
X-Webhook-Timestamp is older than 5 minutes. Ensure your server clock is synchronised via NTP — clock drift will cause valid requests to be incorrectly rejected.Duplicate detection is implemented
Duplicate detection is implemented
Process the same
X-Webhook-Id twice and confirm the event is not processed twice.Endpoint responds within 500 milliseconds
Endpoint responds within 500 milliseconds
Confirm under normal load your endpoint returns
200 well within the timeout.Unknown fields do not break parsing
Unknown fields do not break parsing
ICP may add new optional fields in future versions. Your parser must not fail on unknown fields.
Business logic is asynchronous
Business logic is asynchronous
Your endpoint stores the event and returns
200 before running any downstream processing.Pause vs Cancel
| Action | What happens | Reversible? |
|---|---|---|
| Pause | Temporarily stops delivery. Can be resumed. | Yes |
| Cancel | Permanently terminates the webhook subscription. | No |
